Benefits
- Allows you to simulate systems you haven't got access to: simulating different types of CPU, hardware, memory, ...
- Sandboxing: allows you to take snapshots of system instances, go back, analyze the differences, monitor the traffic or low-level hardware communications
- Security & Honeypots: isolate the suspicious processes inside a virtual machine, escaping from the virtual machine is extremely hard for the attackers
Software
- Bochs: free x86 virtual machine
- PearPC: shell for running Mac OS X PowerPC on Intel
- VMWare: Virtual machine for intel PCs (propriatery with free demo)
- Win4Lin uses the original Windows DLL combined with a compatibility layer to run Windows applications on Linux
- Wine is a complete rewrite of Windows DLL allowing a lot of Windows applications to run on Linux
- linux vserver
- User Mode Linux: run more Linux instances inside itself, in user mode
- Xen: runs NetBSD, Linux and FreeBSD concurrently on x86 with low overhead
- MacOnLinux: Run MacOS Applications on a Mac running Linux
Examples
It is possible to run all of the above concurrently on the same machine!
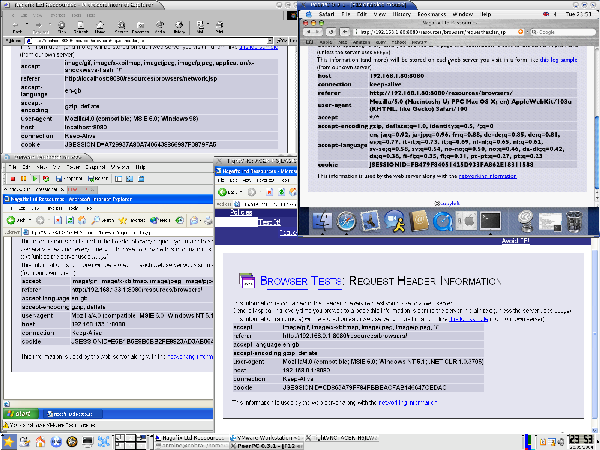 Here we have 4 different ways of running non-native software (on a Linux desktop):
Here we have 4 different ways of running non-native software (on a Linux desktop):
- Top-Left: InternetExplorer running through WINE
The software runs using an emulation layer which implements the Windows DLLs required to run IE - Top-Right: Safari running inside a PearPC emulation
All the software runs on a virtual machine with a simulated PowerPC CPU - Bottom-Left: InternetExplorer running inside Windows XP, using a VMWare virtual machine
All the software runs on a virtual machine which uses the real CPU - Bottom-Right: VNC connection to another machine which runs InternetExplorer inside Windows XP natively
All the software runs natively on the other machine, only the display, mouse and keyboards clicks are fowarded to this window
There are many other ways of forwarding and simulating other systems, most notably the X protocol (native or through an ssh tunnel), serial consoles, video capture..
 Virtualisation
Virtualisation
 copyleft
copyleft